“Help, my WordPress based photography site was infected with malware!”
“Help, my WordPress based photography site has been blacklisted by Google!”
“Help, my WordPress based photography site has been hacked by someone and won’t work!”
If any of the these statements apply to you, then this is a post for you.
[alert color=”red” icon=””]Disclaimer: Though this post is for photography related websites hosted on WordPress, much of what I’ve detailed here is applicable to really any kind of WordPress driven blog. So even if you aren’t a photographer – but you own a website – this is still applicable to you!.[/alert]Preface
My wedding photography website (this one, http://arjunkarthaphotography.com) was infected by “malware” a couple of weeks ago. I consider myself moderately skilled when it comes to web tech – and this turned out to be a something I had never encountered before. What followed was a very frustrating experience that had me learn more about how websites work than I care to know. What was worse, my website had a big RED warning sign on the front page (that prevented anyone from getting in) which looked decidedly scary. My website traffic went down to zero almost overnight. As a result of this the enquiries stopped and I started losing potential business. All in all my website went through various stages of health troubles for a little over two and a half weeks – which literally translates into thousands of potential leads lost (on average I receive around 15-20k visitors a month). I (and other professionals like me) depend on my website as a major pillar in showcasing my work to potential clients, and not having it around was like trying to go upstream in a canoe without a paddle. I’m going to start this post with what happened, and some of things I did to fix it If you’re a photographer, a blogger or anyone with a WordPress driven website, and whether you’re infected yet or not – security is something you need to learn. I hope this post helps!
What happened
On the 23rd of September, 2014 I woke up one morning to read this:
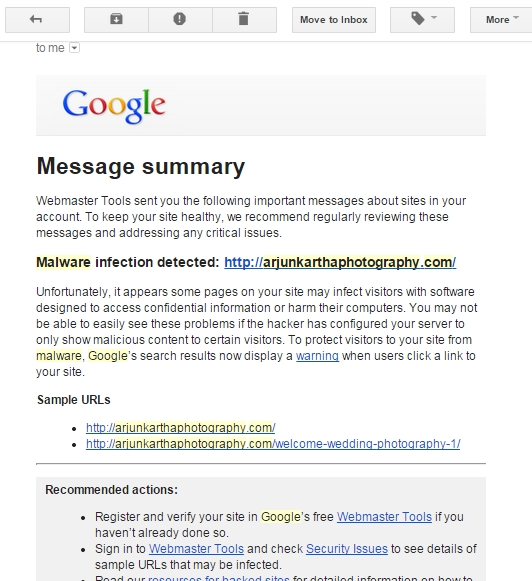
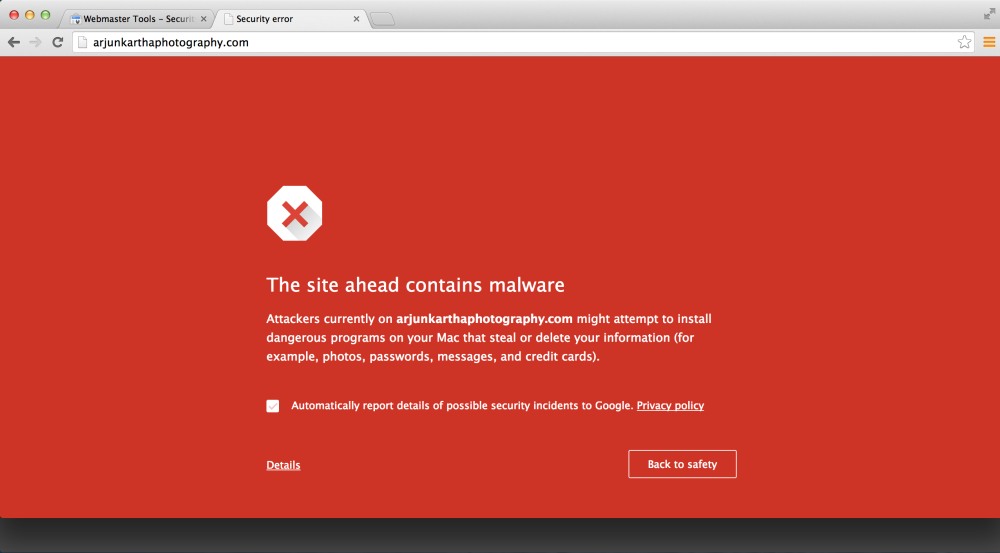
I dismissed it for a bug and didn’t’ really pay much attention to it – until I checked the website and found this horrible screen of death:
I immediately dropped everything else and tried accessing the website from a couple of other computers (and called a few friends in different cities to try too) and it seemed pretty clear that the ban on the website was global. The resources provided by Google soon proved ovewhelming (Google: you seriously need to dumb down your “help” pages). After a couple of hours of research, it seemed there were two possible things that could have happened:
Scenario 1: Someone was deliberately messing with me. Somebody with enough tech skills (or more than me at the very least) had managed to find some sort of loophole in the website and had messed things up with the deliberate intent of making the site go down (or worse, harm my SEO and Page Rank standings)
Scenario 2: An automated attack of some sort had happened – a bot roaming the internet had found the website, found a security loophole – and carried out some sort of hack which benefited the creator of the bot in some fashion. How, I don’t really know – but I believe this happens.
Whatever it was, it needed fixing. I restored the website from a backup, and applied to Google for the ban to be lifted. It was, only to be back the next day. I should have figured that whatever channel the attacker had used to compromise the site would still be open, so that really wasn’t very smart and was a fairly quickfix solution. I tried a variety of freemium tools to try and fix it (malware scanners, plugins that supposedly “harden” the website and so on and so forth) but nothing really worked. This went on for nearly two weeks – where I’d manage to clean the website – only to have it go down again. This took up a substantial amount of my time, which is really something I don’t have much of. I’d have to suspend actual “work” to tend to fixing the website – and in the process I’m glad to say I’ve learnt a lot. All-in-all, here are my recommendations in case you find yourself in the same scenario – or if you want to protect yourself in the best way possible.
How to recover from a malware infection or a hacked WordPress install
Honestly, I don’t think anything short of government level security (and I’m talking snipers and SWAT teams here) will really keep out a determined enemy. Realistically though I’d imagine though that my poor ‘ol website isn’t worthy for an enemy to spend time and resources to do damage to. I’m assuming you don’t have state secrets locked away in your website either, else I’d really recommend you stop reading this and hire an expert!
1. Are you really infected? Determine the level of damage. Here are a couple of ways you can do it:
Copy paste this URL and change the last bit where is says “site=arjunkarthaphotography.com” to “site=yourswebsite.com”
[box title=””]http://www.google.com/safebrowsing/diagnostic?site=arjunkarthaphotography.com [/box]
2. If you are infected, realise you’re screwed. These type of things are really maleficent, and from the way I understand it – once a website is deemed vulnerable, it instantly comes under attack from other malware-oriented attackers too. You need to clean out your website fast. Double check the state of the infection by using the (free) Sucuri site checker: http://sitecheck.sucuri.net/
3. You now need to clean out your website, and FAST. Dealing with malware manually is way beyond my comprehension level, but I believe that if you’re sufficiently skilled, you can go through all the lines of code to find the infected bits and remove them one-by-one. I neither had the time or inclination to do that – so I highly recommend getting an expert to do it for you. I recommend sucuri.net – they really seem to know what they’re doing, and on top of that – I am absolutely blown away by their fantastic customer service. You can choose an appropriate plan for you from their pricing page here: http://sucuri.net/website-antivirus/signup
4. You have to also realise that security is YOUR problem. Services like sucuri.net – though fantastic – will only CLEAN it up for you. You still have to find the source of the infection and deal with it. I am really not sure what the source of my problems were, because I did a lot of things – one of which seemed to have worked. There are several things you can consider:
a. Do you have multiple websites? If yes, are they co-hosted? (In other words, do you have a single FTP access to all of them?) For example, are they all located in /httpdocs/yourwebsitename(s) or some such path? If so, a malware infection in one can jump to ALL of them which is going to cost you a pretty penny. You need to invest in having them sandboxed from each other so that one infection doesn’t result in ALL your websites going on. (On an aside, yes – ALL my websites subsequently went down. Some of the websites I had co-located were arjunkartha.com (my commercial photography work), food-dee-dum.com (PK’s food blog), praerakartha.com (PK’s commercial portfolio) and a couple of others.
b. Hide your admin panel. (yourwebsite.com/wp-admin shouldn’t be accessible. Plugins like WordPress better security will help.
c. Harden your WordPress Installation. This means you need to make certain core directories within WordPress non-executable by 3rd parties, as well as protect your htaccess file. Plugins like WordPress WordFence will help.
5. This should probably be further up the list, but change ALL your passwords. And yes, make them unique. Use cryptographically secure passwords (at least 15 characters with random letters and special characters to make them more robust). Remember, when I say ALL your passwords – I also mean your database password, your server admin password, your host’s admin panel password and last and not the least, your WordPress password. There are a lot of online password manager tools that you can use – Lastpass is my favourite.
6. BACKUP! This seems intuitive, but it’s something that I find really challenging on a day-to-day basis. There are broadly two things you need to backup – your wordpress database, and your wordpress /wp-content folder. There are various backup plugins (some free, some not so free) that do a decent job of this. BackWPup is a good choice – and offers a plethora of choices on where to store your backup. DO NOT store your backup on the same server where your website stays – that nullifies having the backup in the first place. You can save your backup on Dropbox (which makes sense) – but if you live in India like me, or have archaic download limits set by your ISP (don’t get me started) this can create havok with your internet bill. I’m still trying to figure out what the best way to do this is.
7. Consider a website firewall. This is a service that will scan EVERYONE who visits your website to check if they mean to do you harm, and hopefully only let the genuine users through. You’ll have to change your DNS settings to send visitors to the firewall first, and then to your website. I recommend using the Sucuri Website Firewall – I had initially feared that this would slow the website down by adding another link to the chain, but thankfully Sucuri works really fast.
8. Get your webhost involved. Submit a ticket that you’re down with malware and see if they can help. I use MediaTemple’s excellent hosting services and their customer support is second to none. MediaTemple has a malware removal service, and I’m sure your host will too. Remember, webhosts don’t like websites with Malware either, and may decide that hosting you is a violation of the terms of service if you don’t clean it out quickly.
9. Last but not the least, KEEP EVERYTHING UP TO DATE! Attackers use security holes in plugins and the WordPress Core files to get inside – making sure that everything is up to date really helps keep people out.
I’m currently limping back to life – I’m not too sure the extent to which the damage has caused my SEO and PageRank to suffer (I know for a fact I’m not performing as well as I once was for certain keywords), and I really hope things come back to normal soon.
Do you have anything to add, or any observations of your own? Say so in the comments, or feel free to get in touch with me!
PS: Was my website intentionally attacked by someone? In the end we’ll never know – but rest assured, I have my suspicions. Cyber security and laws get stronger by the day – and if you’re the person who is behind all this, remember that what goes around comes around.
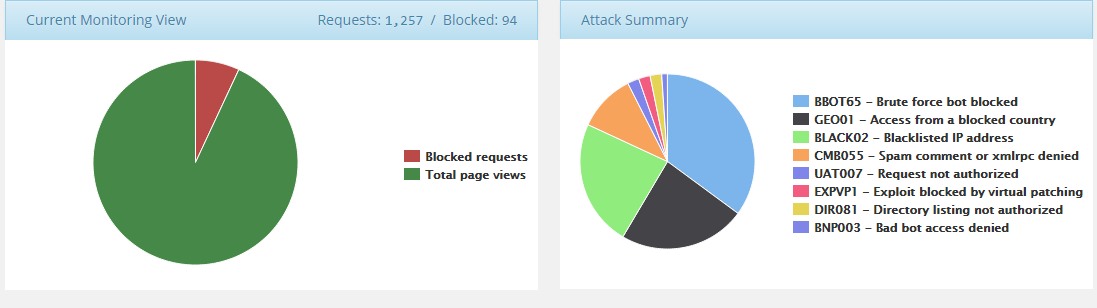
PPS: Cyber attacks are VERY real. I was shocked when I discovered just how much. All websites – this one, and yours included – face literally hundreds of attacks every day. It just takes one to get through to screw with your life. I’m a visual person, and here is one small snapshot (12-hour range) that shows you just how many no-do-gooders can actually try and screw with you in TWELVE HOURS!



Add a Comment